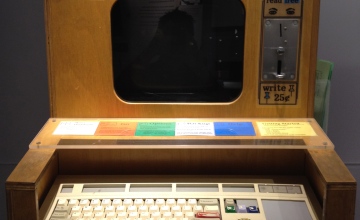
Slow Networks Experiment 5: very short range over-air transmission
Continuing on from “Slow Networks Experiment 1: Over-Air Tranmission,” “Slow Networks Experiments 2 & 3: VHF Radio Transmission,” and “Slow Networks Experiment 4: Videotelephony,” this time we played with a strange and relatively recent entrant to the home security market: the X-10 Wireless video sender which we believe came out in about 1998. This is a puzzling […]
Read More…